- Edited
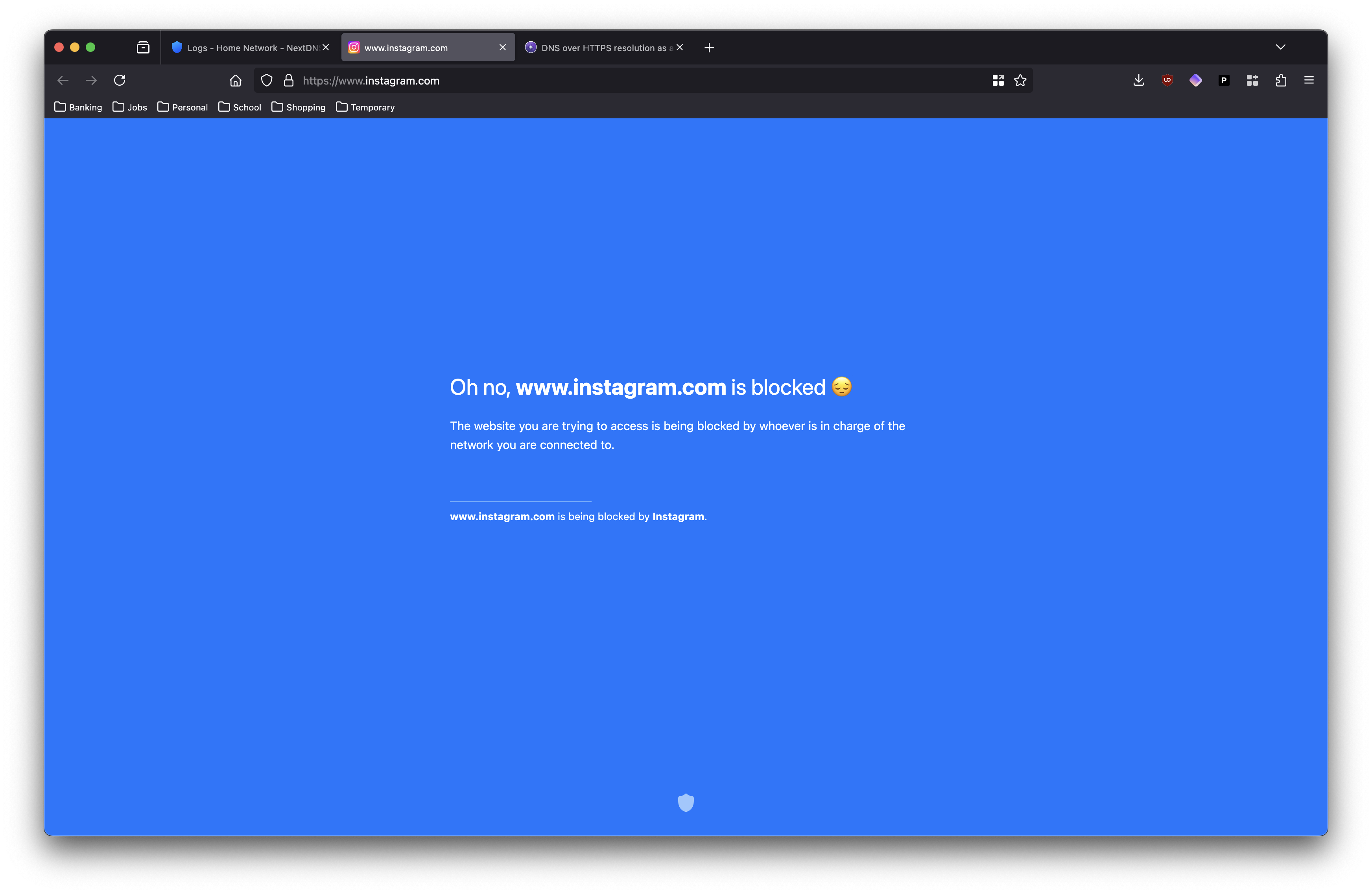
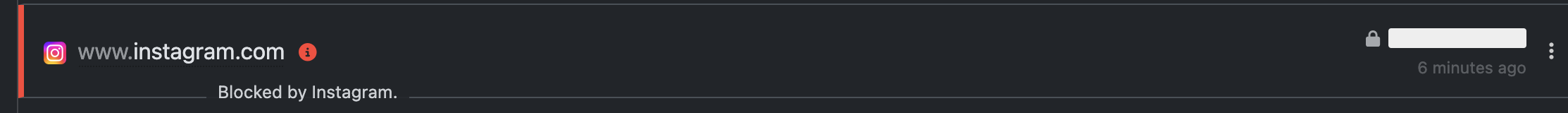
I suspect that the static DNS in MacOS can be hijacked by some of the more aggressive ISPs, since DNS over 53/UDP is unauthenticated. Some US ISPs (example, another example) have been known to intercept 53/UDP traffic, even not to their own IP addresses, to deliver ads to users.
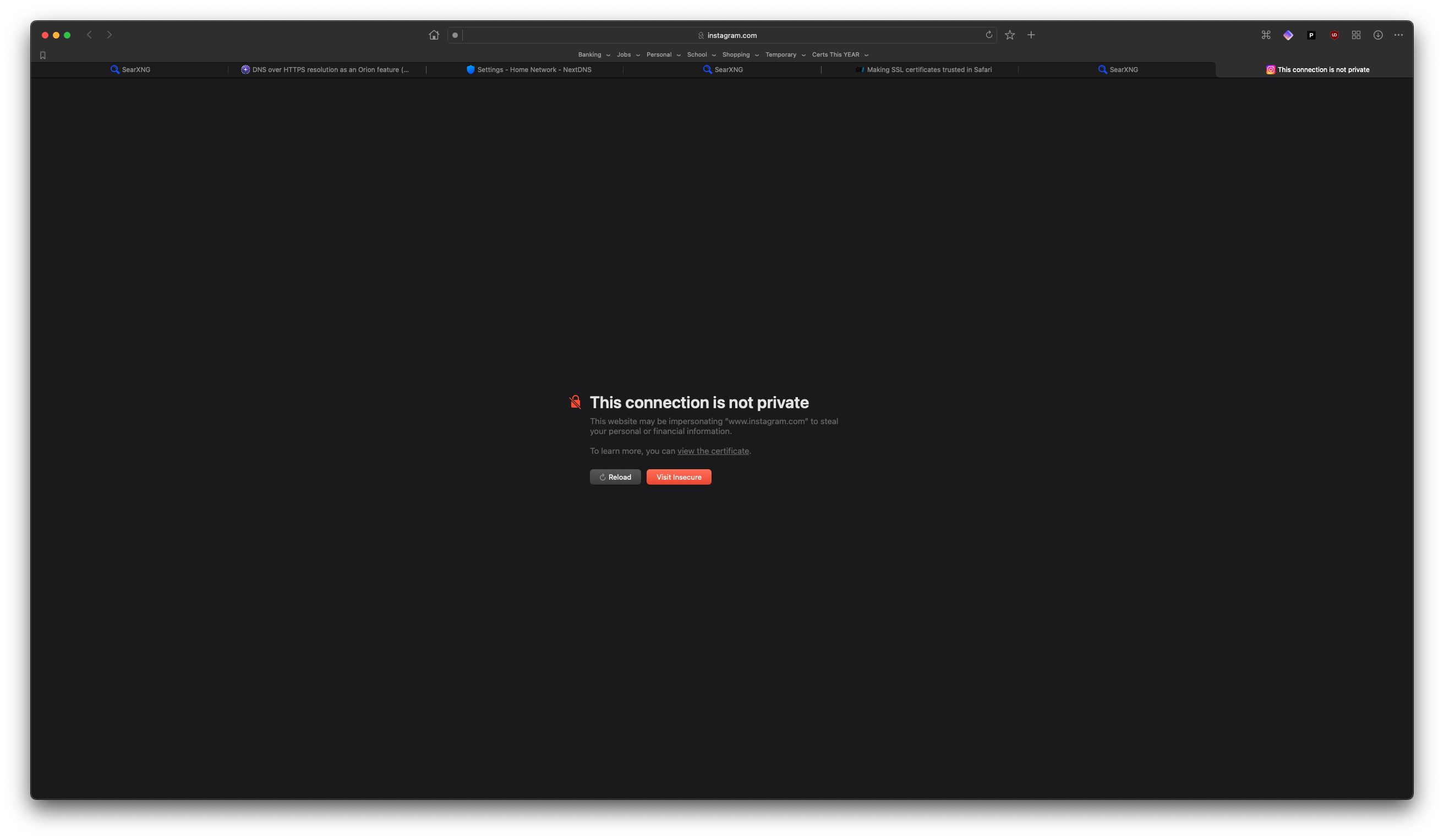
That's not to say it's a browser's responsibility to fix this (actually hijacking 53/UDP and issuing your own responses as an ISP is the real problem), but simply setting a regular UDP DNS server won't necessarily prevent hijacking, unless I've missed something. UDP is not session oriented, and the DNS protocol lacks any verification method, so an ISP or router can intercept and respond to DNS "undetected". You're then relying on HTTPS to alert you if something goes awry.
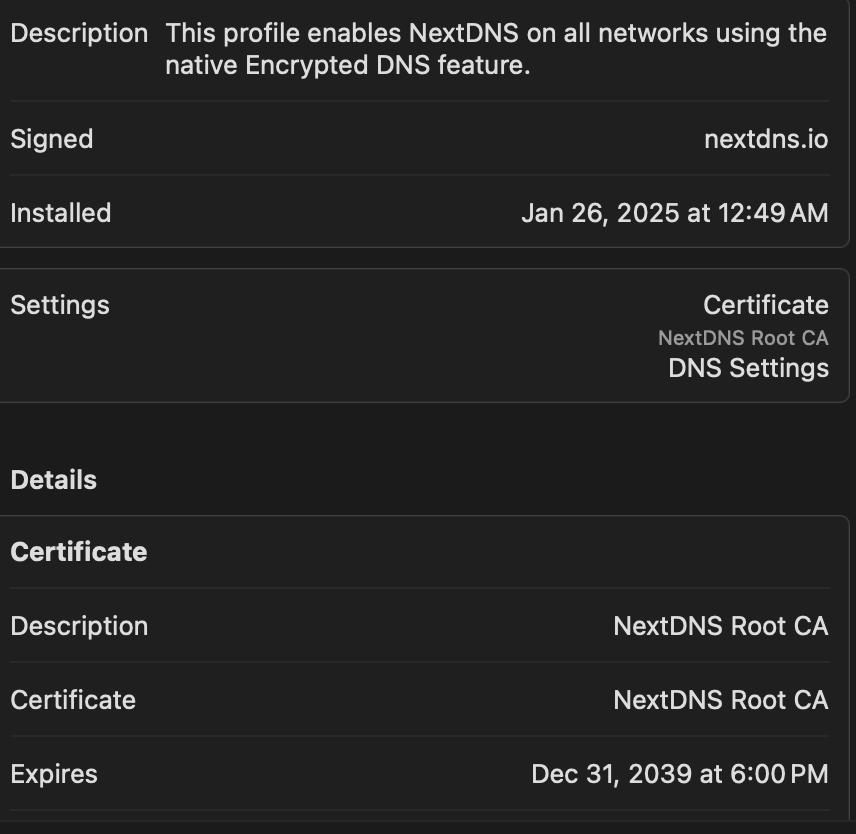
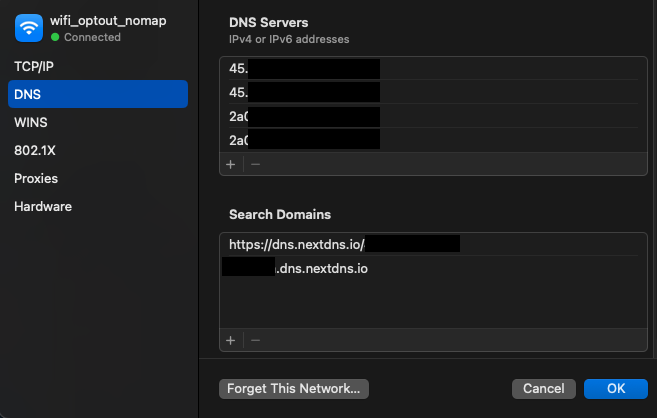
You can set a DNS over TLS/HTTPS setting via a mobileconfig profile, but that will not work if you use a (Mac OS integrated) software firewall like littlesnitch or Lulu.
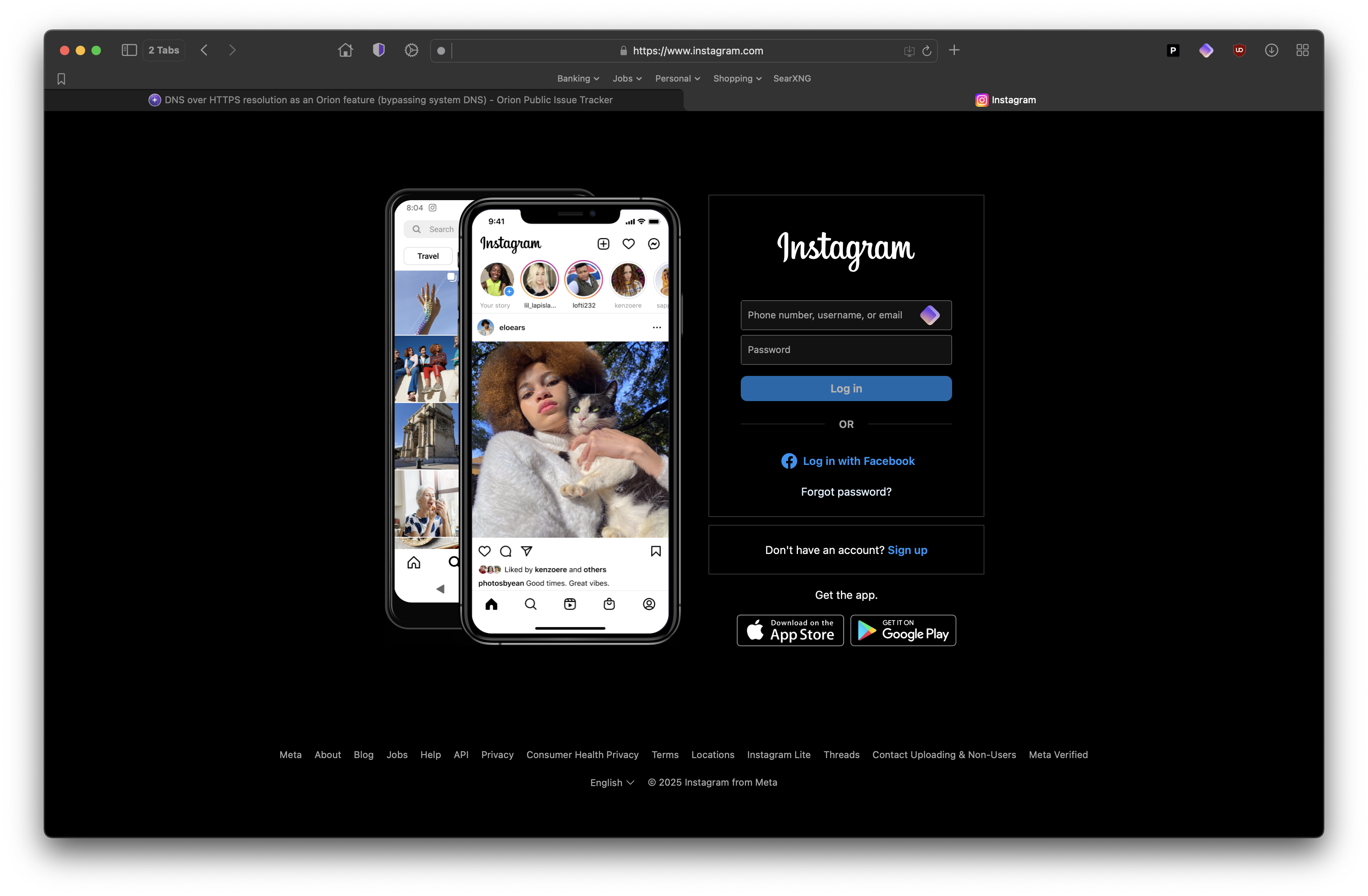
Firefox lets you opt in to DNS over HTTPS as the per-app DNS resolution provider, which can help users escape aggressive ISP hijacking (or just someone who wants to use their own resolver).